Work site security requirements
Learn how the Contract Security Program will guide your organization through the requirements to secure your work site and obtain a document safeguarding capability.
On this page
- Why you need to secure your work site
- Site inspections
- Security orders for personnel
- Access controls
- Security markings
- Destruction and shredding
- Minimum standards for storage, transmittal and destruction
- More information
Why you need to secure your work site
A secure work site is designed to prevent, delay and respond to unauthorized access to sensitive work sites, information and assets.
If your organization is required by contract to store sensitive government information and assets, you will need to obtain a document safeguarding capability through the Contract Security Program.
Site inspections
The program will conduct a site inspection before granting clearance for document safeguarding capability. This will identify what is required to secure your work site, information and assets.
Before the inspection—what to expect
In preparation for the inspection, the field industrial security officer with the program will review the following documents:
- security requirements checklist
- request for private sector organization screening
- contract security clauses
- statement of work
You will be asked to review and complete a security guideline package, the required forms, and a pre-inspection questionnaire. The field industrial security officer will also request a detailed floor plan in order to perform the security inspection.
During the inspection—what to expect
Although there is no cost for the inspection, organizations must pay for the cost of any equipment or construction required to safeguard information and assets at their work sites.
The field industrial security officer will identify:
- potential targets or risks for physical attacks
- intrusion detection systems
- physical security zones in accordance with the federal Operational Security Standard on Physical Security
- how information and assets are handled
Photographs
During the inspection, the field inspection security officer will require authorization and access from your organization to photograph the following:
- all interior and exterior access points, including locking hardware
- storage cabinets and their location
- access control doors to operations or security zone (if applicable)
- server room(s)
After the inspection—what to expect
Inspections may be conducted at any time throughout the life of the contract. If your organization does not comply with contract requirements, security clearance may be denied or terminated.
Your organization can begin work on the contract once the:
- inspection process is complete
- organization has been notified in writing that they possess the required security level
Security orders for personnel
Security orders are required for organizations with document safeguarding capability. It must be submitted to the field industrial security officer before being granted clearance.
Security orders are a document that your organization will create and use to:
- inform employees of their responsibilities
- prevent unauthorized disclosure, destruction, removal, modification or interruption of sensitive government information and assets
It must state that employees:
- may access sensitive information and assets
- only if they have received personnel screening to the appropriate level and have a valid need-to-know, meaning they need to access and know information in order to perform their duties
- are responsible for controlling access to their area and for ensuring that unauthorized persons do not gain access
- if they work with sensitive information and assets
All employees of the organization are required to carefully read these security orders before signing the acknowledgment at the end of the document.
Access controls
Access controls are a type of physical security used to safeguard information and assets. The program provides guidance and advice on what types of access controls are required for specific work sites.
Some access controls include:
- progressively restricted security zones
- locked doors
- access control systems
- intrusion alarm systems
- approved safety containers
Organizations must ensure that all employees, contractors and subcontractors such as cleaners and maintenance workers are properly cleared and are escorted at all times when they enter security zones.
Storage and cabinets
The field industrial security officer from the program will provide storage recommendations. If necessary, the field industrial security officer will assist you in ordering cabinets approved by the Royal Canadian Mounted Police (RCMP). These cabinets are required for storage of classified and Protected C federal government information and assets.
Floor plan and hierarchy of zones
A detailed floor plan must be completed before an inspection can take place.
Your detailed floor plan should identify the following:
- all exterior and perimeter access points to the facility, including doors and windows (ground level)
- all interior and access control points within your facility (operations zone and security zone)
- all locations where protected and classified material, information and assets will be viewed, processed, produced or stored
- all restricted areas
- location of storage cabinets and temporary holding areas
- location of any intrusion alarm components such as motion sensors, keypad, door contacts, closed-circuit television
- location of servers, information technology systems and peripherals
You will need to create a hierarchy of zones to control who can, and cannot, access sensitive information and assets at your work site. These zones must be shown on your floor plan, as illustrated in the images below.
Organization of zones and example of a floor plan
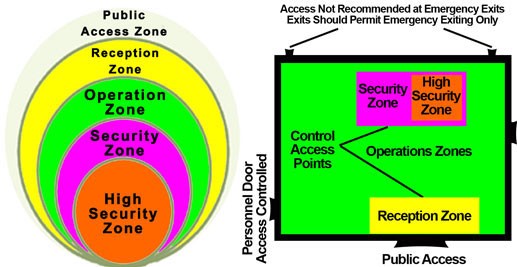
Text description of the organization of zones and example of a floor plan
The organization of zones is depicted by circles. The outer circle is the largest and it encloses the other circles. As the circles get smaller, the security requirements for the zone increase.
The outermost circle represents the public access zone. This is an area where the public has unimpeded access, such as the grounds surrounding a building or its public corridors.
The second outermost circle represents the reception zone. This is an area where the transition from a public zone to a restricted-access area is demarcated and controlled.
The third outermost circle represents the operation zone. This is an area where access is limited to personnel who work there and to properly-escorted visitors, such as a typical open office space or an electrical room.
The fourth outermost circle is also the second innermost circle. It represents the security zone. This is an area to which access is limited to authorized personnel and to authorized and properly-escorted visitors, such as an area where secret information is processed or stored.
The innermost circle represents the high security zone. This is an area to which access is limited to authorized, appropriately-screened personnel and authorized and properly-escorted visitors, such as an area where high-value assets are handled by selected personnel.
The example of a floor plan is depicted by a bird’s-eye view of a rectangular room. The room contains the following zones:
- operation zones
- a reception zone
- a security zone within the operation zones
- a high security zone within the security zone
Access to the security zone is for personnel within the operation zones only. The high security zone is contained within the security zone. Access to the high security zone is restricted to personnel within the security zone.
Access in and out of the room is provided by the following access points:
- a doorway for public access
- leads immediately to a reception zone inside the room
- access beyond the reception zone is restricted by a control access point
- a personnel door that is access-controlled
- access in and out of this door is for personnel within operation zones only
- emergency exits, where access is not recommended and should permit emergency exiting only
- access out of this door is for personnel within operation zones only
More information about security zones
Learn more about:
- hierarchy of zones in the federal Operational Security Standard on Physical Security
- applying physical security zones (Royal Canadian Mounted Police)
Security markings
Information, whether paper or electronic, should be marked to identify it as protected or classified. Organizations should follow government standards for marking protected and classified information.
Destruction and shredding
Sensitive information and assets are destroyed at the end of their life cycle to preserve their confidentiality. This is required for original documents, copies, drafts and notes—any document that includes protected and classified information.
Shredding
Protected shredding capability
- Organizations can shred protected information at their work site using shredding equipment purchased from an office supply store
Secret shredding capability
- For paper, the shredder must be approved by the RCMP
- For information technology, the shredder must be approved by the Communications Security Establishment
Classified shredding capability
- Organizations must use the services of a company with classified shredding capability, and obtain a certificate of destruction once completed
Protected C, Top Secret, COMSEC, NATO and foreign classified information and assets
- Return to the program for disposal or shredding
Shredding facilities
The Contract Security Program inspects shredding companies annually. They must be cleared for shredding capability to the level of the information being stored at their facility.
Mobile shredding
Mobile shredding trucks can be approved to shred protected level information and higher if they meet RCMP standards. In addition, cleared employee of the organization must be present to:
- accompany the documents at all times
- watch the entire destruction process
- inspect the shredded waste
The company security officer (CSO) must ensure that the shredding company is cleared to the appropriate level with the program.
A certificate of destruction must be obtained from the shredding company after the materials are destroyed.
Incineration
Destruction by incineration may only be done by an RCMP-approved incinerator.
Minimum standards for storage, transmittal and destruction
Protected A
Storage
- Paper: Lock in an operations zone, such as in a locked overhead bin, locked drawer or locked office
- Electronic: Save on a secure network drive
Transmittal
- Facsimile: Send and receive by regular facsimile in an operations zone
- Email: Send on a secure internal network
Destruction
- Paper: Use a commercial shredder, up to a maximum of 10 metres
- Electronic: Delete files and empty recycling bin
Protected B
Storage
- Paper: Store information in a locked cabinet in an operations zone
- Electronic: Save on a USB stick, external hard drive or CD and store in a locked cabinet in an operations zone
Transmittal
- Facsimile: Send and receive by regular facsimile in an operations zone with physical controls at both ends of the facsimile transaction
- Email: Use public key infrastructure (PKI) encryption or other approved encryption
Destruction
- Paper: Use an approved type III shredder, which reduces paper fragments to a maximum of 2 mm x 15 mm
- Electronic: Contact the Contract Security Program
Protected C
Storage
- Paper: Store information in a RCMP-approved security container in a security zone
- Electronic: Store information in a RCMP-approved security container in a security zone
Transmittal
- Facsimile: Send and receive by secure facsimile and telephone equipment with an approved encryption device in a security zone
- Email: Do not use email
Destruction
- Paper: Use and approved type II shredder, which reduces paper fragments to a maximum of 1 mm x 14.3 mm
- Electronic: Contact the Contract Security Program
Confidential
Storage
- Paper: Store information in a RCMP-approved security container in an operations zone
- Electronic: Must be stored in a RCMP-approved security container in an operations zone
Transmittal
- Facsimile: Send and receive by secure facsimile and telephone equipment with an approved encryption device in a security zone
- Email: Do not use email
Destruction
- Paper: Use an approved type III shredder, which reduces paper fragments to a maximum of 2 mm x 15 mm
- Electronic: Contact the Contract Security Program
Secret
Storage
- Paper: Store information in a RCMP-approved security container in a security zone
- Electronic: Store information in a RCMP-approved security container in a security zone
Transmittal
- Facsimile: Send and receive by secure facsimile and telephone equipment with an approved encryption device in a security zone
- Email: Do not use email
Destruction
- Paper: Use an approved type II shredder, which reduces paper fragments to a maximum of 1 mm x 14.3 mm
- Electronic: Contact the Contract Security Program
Top Secret
Storage
- Paper: Store information in a RCMP-approved security container in a high security zone
- Electronic: Store information in a RCMP-approved security container in a high security zone
Transmittal
- Facsimile: Send and receive by secure facsimile and telephone equipment with an approved encryption device in a high security zone
- Email: Do not use email
Destruction
- Paper: Use an approved type II shredder, which reduces paper fragments to a maximum of 1 mm x 14.3 mm
- Electronic: Contact the Contract Security Program
More information
- Consult the federal Operational Security Standard of Physical Security
- Learn about the following in the Industrial Security Manual: